Amazon Nitro North: Secure, Sovereign, High-Performance AWS
If you’ve ever heard someone in a meeting say “Nitro” and just nodded like you totally knew what that meant… this is for you.
And no, Amazon Nitro North is not a new AWS region somewhere above Santa’s workshop. It’s more of a design pattern—a mindset:
Using Nitro-based AWS infrastructure in northern, sovereignty-obsessed regions (U.S., Canada, Nordics, EU North, GovCloud, and emerging EU sovereign regions) to get security, performance, and data residency without losing your sanity—or your auditors.
Let’s unpack what the AWS Nitro System actually is, why it matters for cloud security and data sovereignty, and how you can weaponize it for your “we really care about data residency” workloads.
1. What Is the AWS Nitro System?
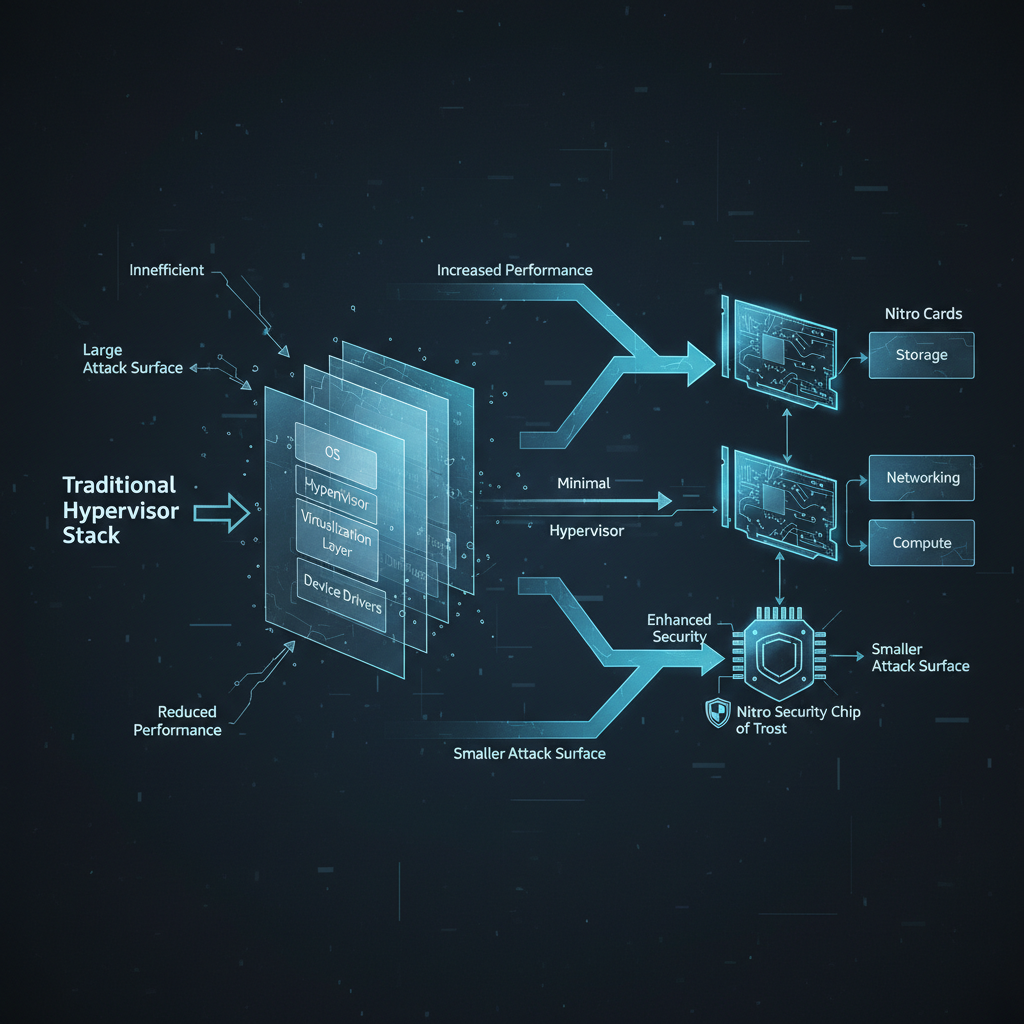
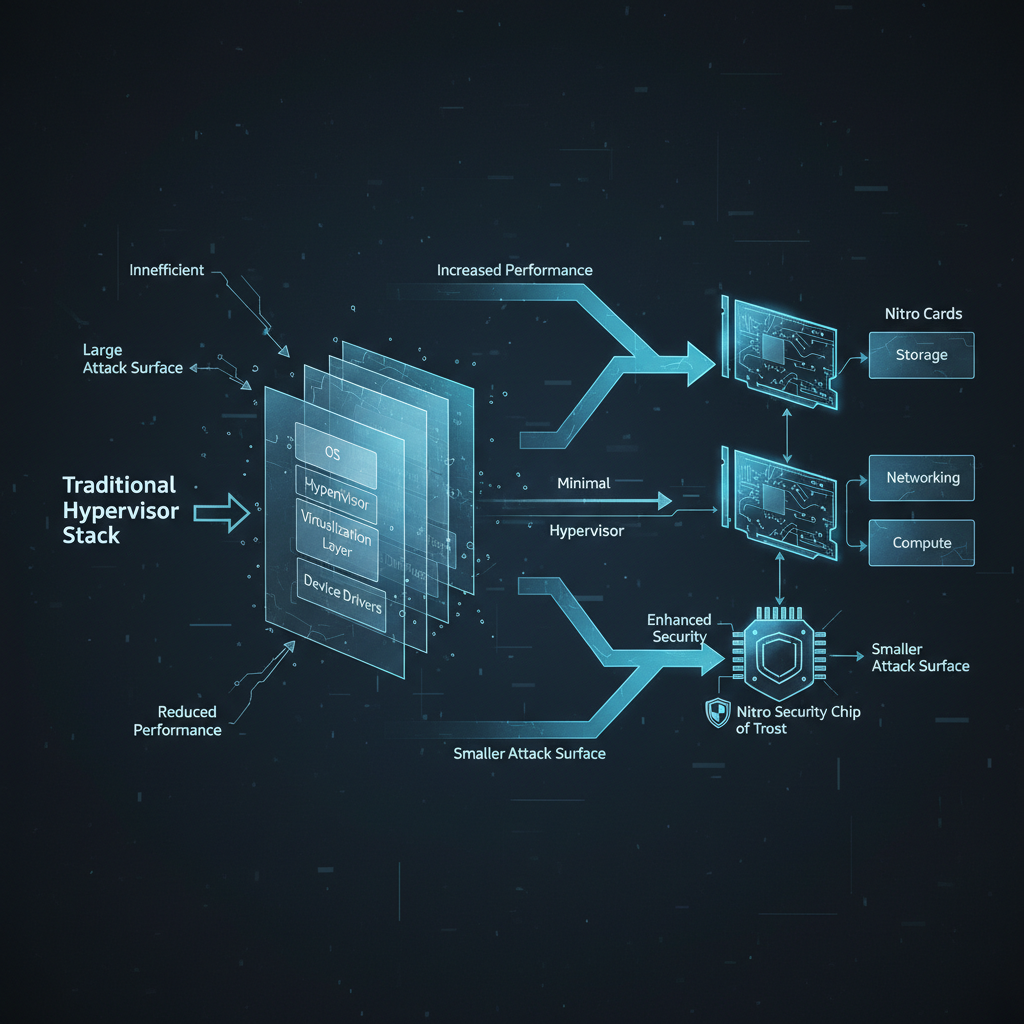
Think of Nitro as AWS looking at the old-school hypervisor stack and saying, “Yeah, no. We can do better.”
Traditional hypervisors try to do everything. Nitro rebuilds virtualization from the ground up, splitting responsibilities into tightly scoped, hardened components. That’s the foundation of Nitro-based AWS infrastructure.
1.1 Nitro Cards: The Specialized Muscle
Nitro Cards are dedicated hardware offload engines. Each card has a specific job and, unlike some of your projects, it actually does it:
- Nitro Card for VPC – handles networking
- Nitro Card for EBS – handles block storage
- Nitro Card for instance storage – manages local NVMe / Nitro SSD
By offloading networking and storage:
- Your host CPU is freed up for your workloads
- You get predictable performance instead of “it’s slow because neighbors” drama
- A big chunk of the previous “hypervisor magic” is now hard-wired and locked down in silicon
1.2 Nitro Security Chip: The Hardware Bouncer
This is the root of trust in the AWS Nitro System.
The Nitro Security Chip:
- Enforces secure boot with hardware-backed verification
- Continuously checks firmware integrity
- Blocks unauthorized firmware changes
- Is designed so even AWS operators can’t log into your instance
Let that last sentence sink in. No “oops, a support engineer SSH’d into prod” scenarios. The architecture literally prohibits administrative access to your instances from AWS.
1.3 Nitro Hypervisor: Diet Hypervisor, Zero Bloat
Nitro uses a minimal KVM-based hypervisor that:
- Only does CPU + memory virtualization and device assignment
- Has no general-purpose OS
- Has no networking or storage stack
Result?
- Tiny attack surface
- Fewer bugs to fear
- Performance that’s “nearly indistinguishable from bare metal” for many workloads
And for a bunch of instance families, you can even go bare metal (*.metal) while still being protected by the Nitro Security Chip.
1.4 What This All Adds Up To
By decomposing virtualization into hardware, firmware, and a tiny hypervisor, the AWS Nitro System:
- Shrinks the trusted computing base (TCB)
- Cuts out operator/admin access
- Frees more CPU and memory for your workloads
- Delivers instances that are fast, cost-efficient, and secure
In other words, Nitro is the invisible secure cloud infrastructure upgrade your workloads deserve, even if your CFO doesn’t appreciate the poetry of ASIC offload.

2. Why Nitro Exists: Escaping the Traditional Hypervisor Swamp
Old-school virtualization (Xen, VMware, Hyper-V) uses a big privileged domain (Dom0, management OS, etc.) to:
- Own the hardware
- Run tons of drivers
- Handle networking and storage
- Expose management APIs
That works, but:
- Big OS = big attack surface
- Drivers and services = bug buffet
- Misconfig or exploit = potential tenant isolation issues
- Hypervisor overhead = wasted CPU/RAM you still pay for
AWS took the “what if we just… didn’t?” approach:
- Move networking and storage to Nitro Cards
- Move trust to the Nitro Security Chip
- Strip the hypervisor down to the bare minimum
That’s why Nitro-based AWS infrastructure is especially attractive in:
- Financial hubs (New York, Toronto, London)
- Government / defense regions (e.g., GovCloud (US))
- Privacy-obsessed northern Europe (Stockholm, Nordics, EU North)
When people say “Nitro in the north” or “Amazon Nitro North,” they’re basically talking about:
Nitro-backed EC2 capacity in regions where data can’t leave, security can’t compromise, and latency can’t suck.

3. Why Nitro Is a Big Deal for Northern (and Global) Workloads
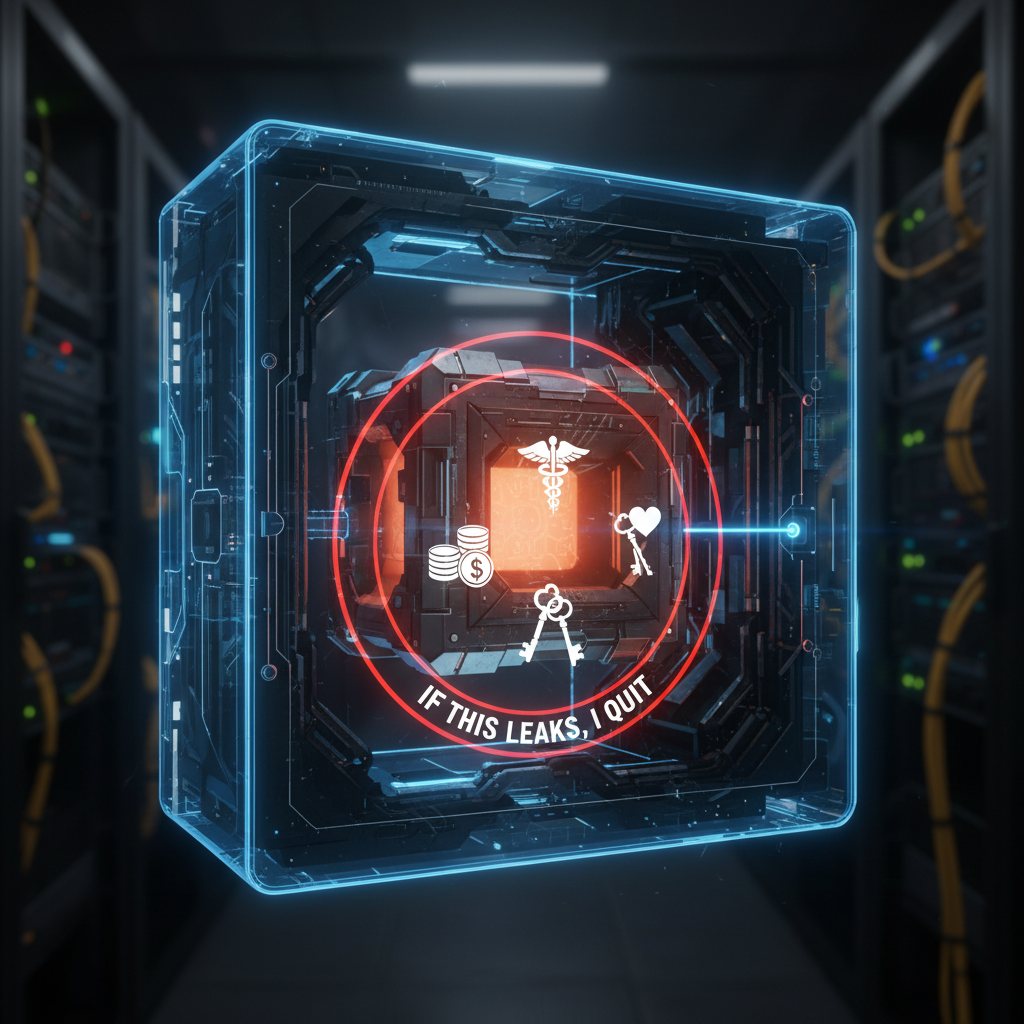
3.1 Security: No-Operator-Access and Locked-Down Control Plane
Nitro’s big flex: AWS operators do not have admin access into your instances.
Practically, that means:
- No secret SSH backdoor for AWS
- No “hypervisor console” for them to peek at your workloads
- EC2 operations (start/stop/attach volume) go through signed, authenticated APIs on Nitro hardware
- Firmware is loaded from encrypted, verified storage on every boot
If your world involves:
- PII
- Financial records
- Healthcare data
- Law-enforcement / national-security workloads
…being able to say “even the cloud provider can’t log in” is extremely helpful when auditors show up with clipboards and suspicion.
3.2 Performance: More Server for You, Less for Overhead
By kicking most virtualization work off to hardware:
- Your instances get more of the host’s CPU and RAM
- Networking and storage are fast and predictable
- EBS and Nitro SSDs can hit serious throughput and IOPS in the latest generations
Perfect for:
- High-frequency trading
- Real-time analytics
- Low-latency APIs and AI inference close to users in North America and the Nordics
3.3 Cost: Performance Per Dollar That Doesn’t Make You Cry
Because AWS can run more efficient, Nitro-powered hosts:
- They operate denser, more efficient fleets
- They can price many Nitro-based instance families more aggressively
- You get more usable resources per dollar (i.e., fewer ghost CPUs eaten by hypervisor overhead)
Pair that with cooler climates and renewable energy in northern regions, and you get solid price/perf plus bonus ESG points.
4. Nitro Enclaves: Confidential Computing for Paranoid Adults
If Nitro is the foundation, Nitro Enclaves are the panic room.
They let you carve out isolated execution environments inside a Nitro-based EC2 instance that:
- Have no external network access
- Have no persistent storage
- Have no direct SSH/shell access (not even for root on the parent)
- Talk only via vsock (a secure local socket) with the parent instance
You also get attestation:
- Prove to an external system that:
- You’re on real Nitro hardware
- The enclave is running the exact expected code/image
This is often tied to KMS, so keys are only released to “good” enclaves.
4.1 Popular Northern Use Cases
You see Nitro Enclaves lighting up in Amazon Nitro North style architectures across:
- Financial services
- Decrypt/process payments
- Hold private keys
- Run risk models on sensitive data
- Healthcare
- Process PHI/PII for analytics or AI
- Run identity matching or de-anonymization securely
- Public sector / defense
- Identity verification pipelines
- Sensitive analytics and intel workloads
These all pair local data residency (e.g., eu-north-1, ca-central-1, GovCloud) with confidential compute. That combo is basically what “Amazon Nitro North” is hinting at: regional sovereignty plus Nitro-backed confidential computing.

5. Nitro and AI: Keeping Your Models and Prompts Out of the Gossip Columns
Welcome to 2024/2025, where every architecture diagram now has at least one box labeled “AI” circled in red.
Nitro is quietly one of the big reasons AWS can say:
- For Nitro-based GPU and accelerator instances (P, G, Trainium, Inferentia, etc.), Amazon personnel can’t see your models or data running on those machines.
So if you’re:
- Running LLM inference on GPUs in
eu-north-1for a Nordic bank - Training healthcare models in
us-east-1for a U.S.-only environment - Doing AI in
ca-central-1under Canadian residency rules
…Nitro is part of the guarantee that your:
- Model weights
- Customer prompts
- Training data
aren’t being snooped, even by the provider.
Combine that with:
- Nitro Enclaves for key management and sensitive preprocessing
- Attestation to prove workloads are running where and how you claim
And you can build:
- End-to-end confidential AI pipelines:
- Data lands encrypted
- Keys are released only to attested Nitro (or enclave) nodes
- Training/inference runs in operator-free environments

6. Designing an “Amazon Nitro North” Architecture
Let’s glue this together into something that looks like an actual platform rather than a cool buzzword mashup.
6.1 Step 1: Pick the Right Region and Instance Families
- Region selection (the “North” part):
- U.S.:
us-east-1,us-east-2,us-west-2, or GovCloud (US) for stricter controls - Canada:
ca-central-1 - Europe:
eu-north-1(Stockholm), plus variouseu-west-*and upcoming northern/EU sovereign regions
These give you low-latency access to northern users and help you meet data residency and data sovereignty requirements.
- U.S.:
- Instance families (the “Nitro” part):
- General/compute: M6/M7, C6/C7, R6/R7 (Intel, AMD, Graviton)
- Memory / DB: R* families, some X* families
- AI & GPU: P*, G*,
trn*,inf* - Bare metal:
*.metalwhen you need low-level control but still want Nitro security
6.2 Step 2: Use Nitro Enclaves Where You Actually Lose Sleep
Good places to start:
- Key management / decryption
- Keys live in KMS
- Only released to attested enclaves
- Payment processing / PII workflows
- Parent instance receives encrypted payloads
- Enclave does decryption + sensitive logic
- Only returns minimal results (tokens, flags, decisions)
Auditors love this pattern because:
- Privileged admins can’t read the raw sensitive data
- You can prove that the enclave is running exactly what you say it is
- Data never leaves your chosen northern region
6.3 Step 3: Turn On NitroTPM and Measured Boot Like a Responsible Adult
Nitro-based instances support NitroTPM, a virtual TPM 2.0 anchored in Nitro’s hardware trust.
Use it to:
- Implement measured boot (hashing boot components as the system starts)
- Verify instance integrity automatically before:
- Handing out app secrets
- Registering nodes into high-trust clusters (payments, KYC, auth, etc.)
This aligns beautifully with:
- NIST
- ISO 27001
- SOC 2
- And every security framework that loves the phrases “root of trust” and “measured boot”

7. Real-World-Style Example: A Nordic Fintech on Nitro
Let’s pretend you’re a fintech in Stockholm. You care about:
- EU data residency
- Banking secrecy
- Regulator-induced insomnia
Here’s your Amazon Nitro North setup in eu-north-1:
- Frontend & APIs
- Run on Graviton-based M7g/C7g (Nitro-backed, cost-efficient, good perf)
- TLS everywhere, PII stripped from logs before storage
- Core Banking / Ledgers
- On R7 instances (memory-friendly)
- EBS encrypted via KMS with region-locked CMKs
- Sensitive Payloads in Nitro Enclaves
- Card numbers, ID docs, etc. only decrypted inside Nitro Enclaves
- KMS keys are released only after enclave attestation passes
- Fraud Detection & AI
- Models train and infer on Nitro-based GPU instances in
eu-north-1 - Training data encrypted at rest, decrypted only into attested Nitro nodes
- Models train and infer on Nitro-based GPU instances in
- Compliance Story
- NitroTPM-based measured boot for key services
- Evidence showing:
- No operator access
- Region-only data residency
- Enclave-based protection of the crown jewels

8. Getting Started with Nitro in Your Own Environment
Action items before this just becomes another “nice blog I read once”:
- Inventory your EC2 fleet
- Spot old, non-Nitro dinosaurs (T2, M3, C3, etc.)
- Plan migrations to Nitro families in your target region
- Pick your “north” (if sovereignty matters)
- U.S.? GovCloud / east / west.
- Canada?
ca-central-1. - Europe?
eu-north-1or another EU region aligned with your laws.
- Choose one sensitive use case for Nitro Enclaves
- Payment tokenization
- Identity verification
- Key management
- Start small: one service, one enclave workflow.
- Turn on NitroTPM + measured boot in your golden images
- Update AMIs / OS configs
- Integrate integrity checks into your secret distribution logic
- Loop in security and compliance early
- Hand them AWS’s Security Design of the AWS Nitro System whitepaper
- Map Nitro features to your controls:
- “No operator access”
- “Secure boot”
- “Confidential compute (enclaves)”
- “TPM-backed attestation”
9. The Big Picture: What “Amazon Nitro North” Really Means
Underneath the marketing-adjacent phrasing, here’s what we’re actually talking about:
- Nitro =
- Nitro Cards + Nitro Security Chip + minimal hypervisor
- No-operator-access design
- Strong isolation + performance close to bare metal
- North =
- Regions like
us-east-*,ca-central-1,eu-north-1, GovCloud, and EU sovereign builds - Data residency, low latency to northern users, and stricter compliance
- Regions like
- Amazon Nitro North (in practice) =
- Architectures that use Nitro-based AWS infrastructure, Nitro Enclaves, NitroTPM, and northern regions to deliver:
- Sovereign, local data processing
- Confidential computing for sensitive and AI workloads
- High performance per dollar
- A secure cloud infrastructure story that makes auditors significantly less grumpy
- Architectures that use Nitro-based AWS infrastructure, Nitro Enclaves, NitroTPM, and northern regions to deliver:
If you care about security, performance, and “our data must stay here” in the U.S., Canada, or Europe, building on Nitro in a northern region isn’t just a nice idea—it’s pretty much the new baseline for modern, sovereign cloud architectures.
Leave a Reply